Page Not Found
Sorry! The page you were looking for is no longer available or the link has expired. If you were looking for a specific product, you can search our store.
While you’re here, take a look through some of our great articles!
Beekeeping basics
<!--
Beekeeping basics
By Charles Sanders
-->
Issue #88 • July/August, 2004
Bees have been managed for their honey production for about 5000 years or so. Especially for the...
Companion Planting
By Beverly Mettot
Issue #81 • May/June, 2003
Companion planting is nothing new, and yet in recent years it has made an extraordinary comeback, not only...
The Best City Garden
By Anita Evangelista<!--
The best city garden
By Anita Evangelista
-->
Issue #103 • January/February, 2007
City gardens and country gardens are differentnot only in the amount of space...
Currants and Gooseberries
By Sylvia Gist
Issue #155 • September/October, 2015
Currants and gooseberries all belong to the genus Ribes (pronounced "rye-bees"). There are varieties of currants and gooseberries...
By John Silveira
Issue #119 • September/October, 2009
Gun control people don't seem to get just how deeply etched into the American psyche gun ownership goes and that the resistance to being disarmed by their own government runs even deeper.
Private arms have been confiscated from the populace in almost every other...
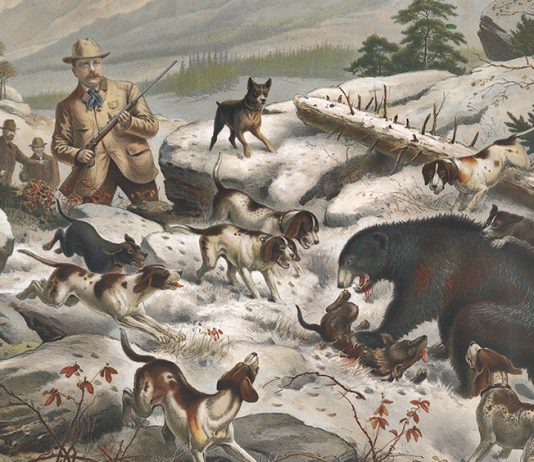
By O.E. MacDougal
November/December 2016, Backwoods Home
I could spend all day coming up with interesting trivia about the Presidents and those who surround them — wives, children, assassins, etc. I could literally fill this magazine with those facts.
The Tallest and Shortest
Let’s start with some common ones. Most school children can...
By Marjorie Burris
Issue #57 • May/June, 1999
My grandmother, Mary Etta Dillman Graham, was one of those frontier women who took life as it came; extremely practical, resourceful and inventive, she was always, always ready to help other women. True to her time and her own modest nature, she never...